DESCRIPTION:
Red Hat Security on Twitter

RHSA-20220927 Red Hat Security Advisory OpenShift Container
.
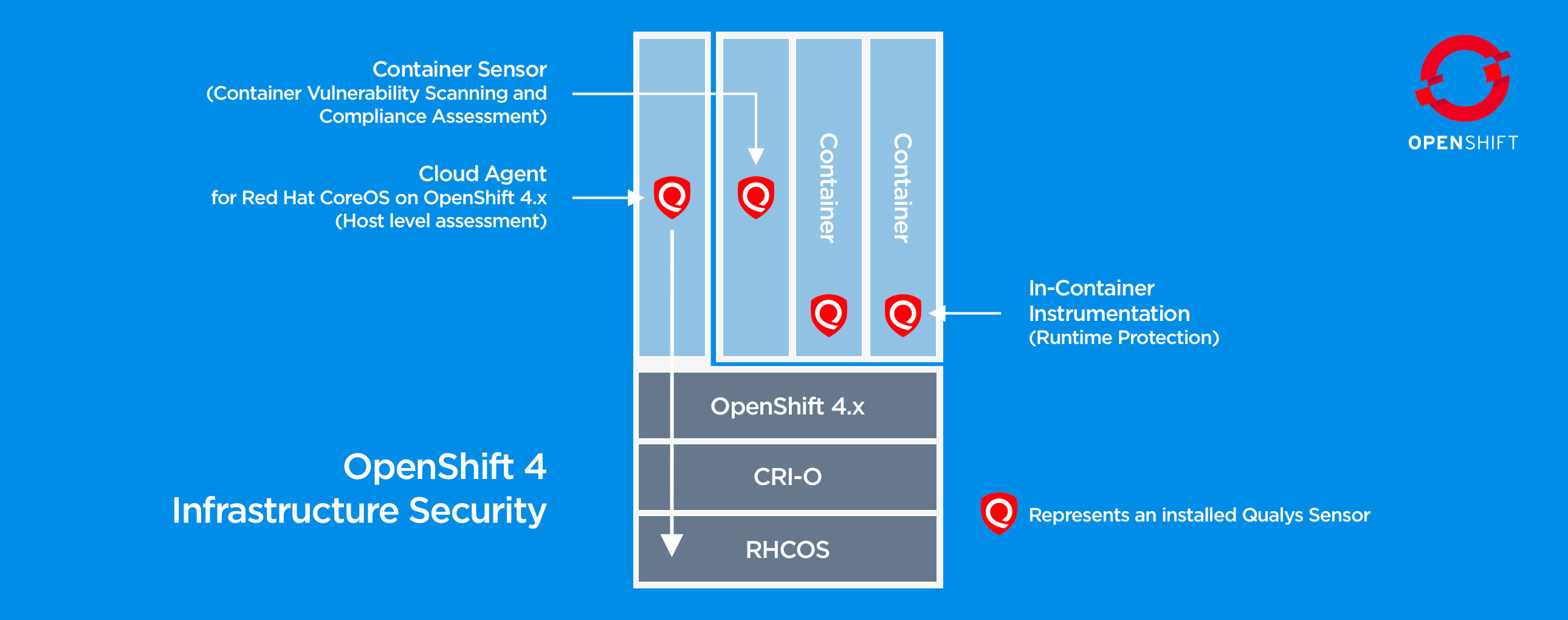
Securing Red Hat Enterprise Linux CoreOS in Red Hat OpenShift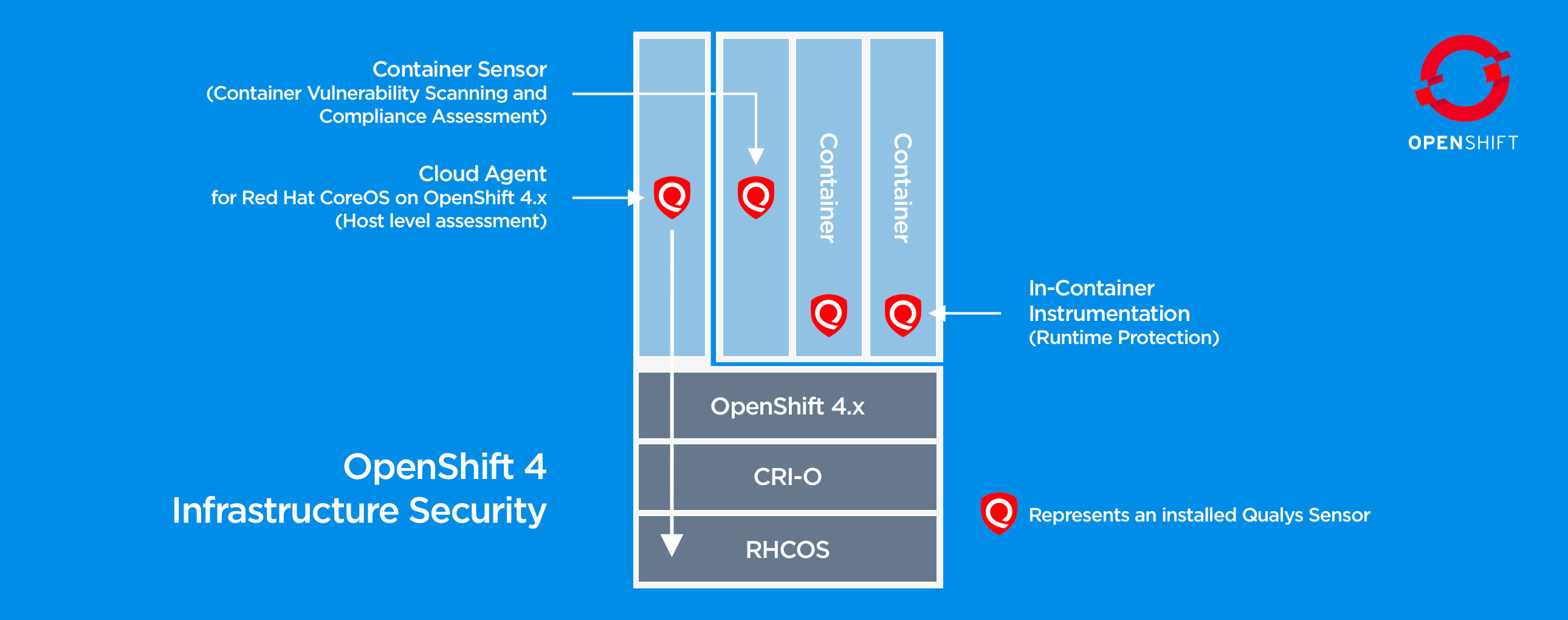 Assessing Red Hat Ansible Automation Platform vulnerabilities
Assessing Red Hat Ansible Automation Platform vulnerabilities Assessing and Monitoring Security Vulnerabilities on RHEL Systems
Assessing and Monitoring Security Vulnerabilities on RHEL Systems Why automate security and compliance
Why automate security and compliance Understanding security audits Documentation for BMC Discovery
Understanding security audits Documentation for BMC Discovery Red Hat Insights Services Demo
Red Hat Insights Services Demo Red Hat Security Advisory 2016-1546-01 – 0dayroot
Red Hat Security Advisory 2016-1546-01 – 0dayroot Happy 15th Birthday Red Hat Product Security Red Hat Customer Portal
Happy 15th Birthday Red Hat Product Security Red Hat Customer Portal Red Hat Product Security Risk Report 2016 Red Hat Customer Portal
Red Hat Product Security Risk Report 2016 Red Hat Customer Portal rhel RH Security Advisory how to interpret Unix & Linux Stack
rhel RH Security Advisory how to interpret Unix & Linux Stack Assessing and Monitoring Security Vulnerabilities on RHEL Systems
Assessing and Monitoring Security Vulnerabilities on RHEL Systems Security Bulletins Red Hat Customer Portal
Security Bulletins Red Hat Customer Portal Assessing and Monitoring Security Vulnerabilities on RHEL Systems
Assessing and Monitoring Security Vulnerabilities on RHEL Systems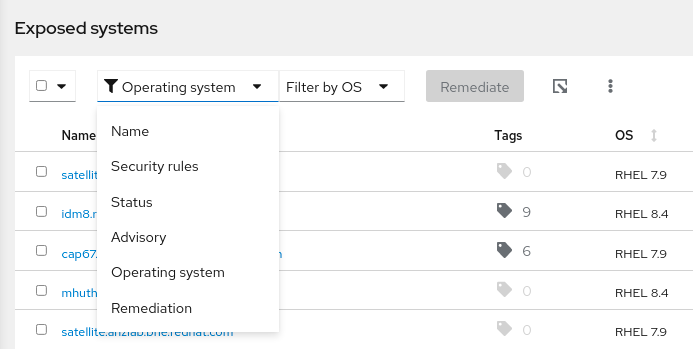

RHSA-20220927 Red Hat Security Advisory OpenShift Container
.

Securing Red Hat Enterprise Linux CoreOS in Red Hat OpenShift
 Assessing Red Hat Ansible Automation Platform vulnerabilities
Assessing Red Hat Ansible Automation Platform vulnerabilities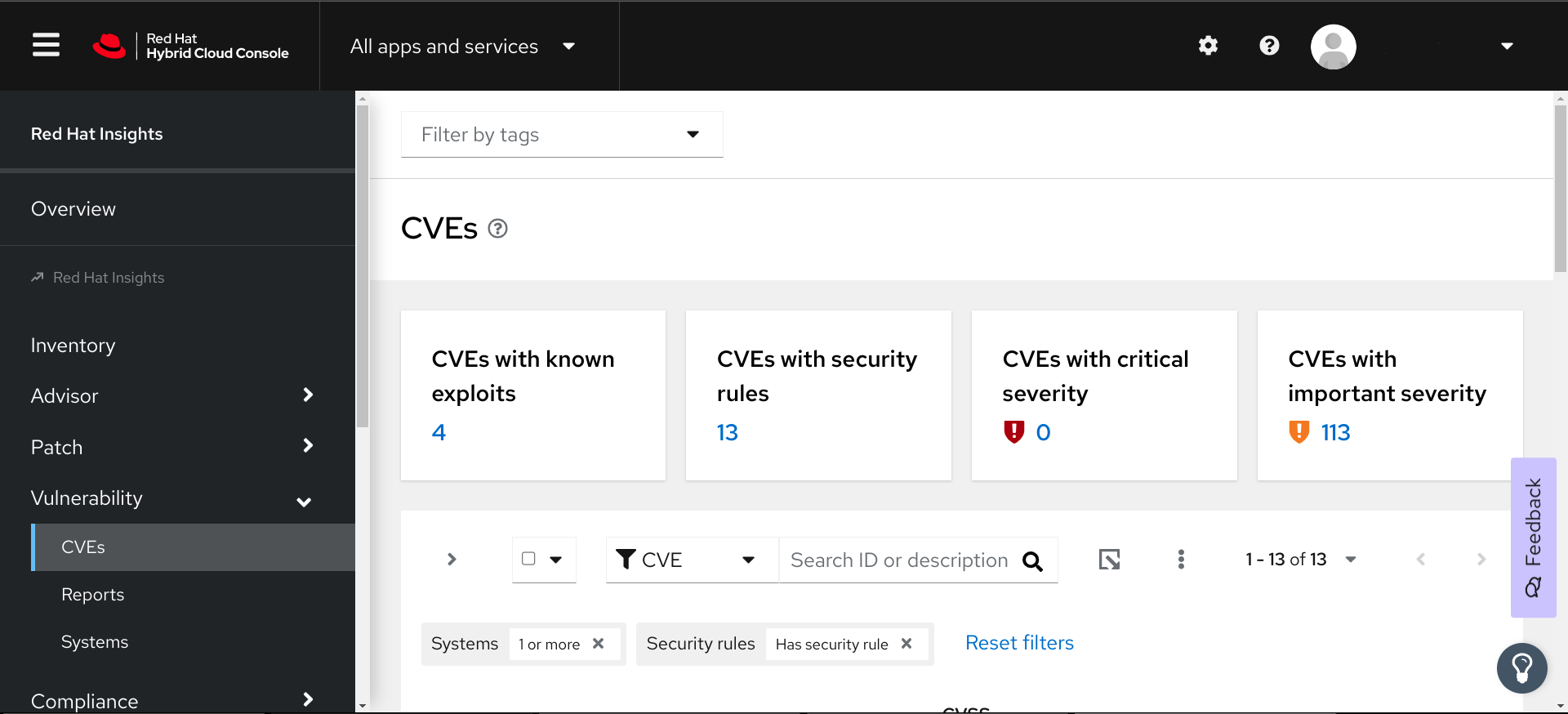 Why automate security and compliance
Why automate security and compliance Red Hat Insights Services Demo
Red Hat Insights Services Demo Red Hat Security Advisory 2016-1546-01 – 0dayroot
Red Hat Security Advisory 2016-1546-01 – 0dayroot Happy 15th Birthday Red Hat Product Security Red Hat Customer Portal
Happy 15th Birthday Red Hat Product Security Red Hat Customer Portal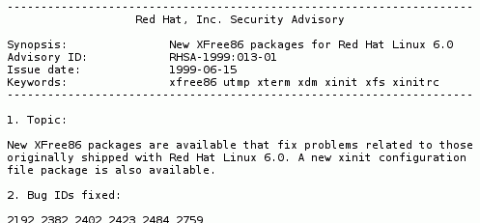 Red Hat Product Security Risk Report 2016 Red Hat Customer Portal
Red Hat Product Security Risk Report 2016 Red Hat Customer Portal rhel RH Security Advisory how to interpret Unix & Linux Stack
rhel RH Security Advisory how to interpret Unix & Linux Stack Assessing and Monitoring Security Vulnerabilities on RHEL Systems
Assessing and Monitoring Security Vulnerabilities on RHEL Systems Security Bulletins Red Hat Customer Portal
Security Bulletins Red Hat Customer Portal Assessing and Monitoring Security Vulnerabilities on RHEL Systems
Assessing and Monitoring Security Vulnerabilities on RHEL Systems
YOU MAY ALSO LIKE:
Customer Also Buy:
PRODUCT REVIEWS:
iPhone XR -
by Omni,
2024-09-16
5/
5stars
RHSA-20220927 Red Hat Security Advisory OpenShift Container
iPhone SE -
by Octavio,
2024-09-13
5/
5stars
Understanding security audits Documentation for BMC Discovery
iPhone 7 -
by Sarem,
2024-09-09
5/
5stars
Red Hat Security Advisory 2016-1546-01 – 0dayroot
iPhone 13 -
by Zymire,
2024-09-06
5/
5stars
Red Hat Product Security Risk Report 2016 Red Hat Customer Portal
iPhone 6 Plus -
by Reinhold,
2024-09-02
5/
5stars
rhel RH Security Advisory how to interpret Unix & Linux Stack
iPhone 8 Plus -
by QuinlynnRahib,
2024-08-30
5/
5stars
Assessing and Monitoring Security Vulnerabilities on RHEL Systems
© 2019-2023 surrogatees.com All rights reserved.